
Warning: Hackers Target Ubiquiti Devices
If your organization owns and operates Ubiquiti devices, you are advised to change your account credentials immediately – regardless of whether you are hosting services on the cloud or not. Additionally, we recommend taking the additional step of enabling two-factor authentication.
According to Ubiquiti Inc., the company became aware of “unauthorized access to certain of our information technology systems hosted by a third-party cloud provider.” An email was sent to all Ubiquiti customers on file to inform them of the breach.
According to the company’s statement, leadership is currently unaware of evidence that might suggest bad actors gained access to any databases that host user data. However, Ubiquiti also acknowledged that the company can’t be certain that exposure hasn’t occurred.
To combat the ongoing threat of cyber fraud when accessing data from your Ubiquiti devices, please change your password regularly and enable two-factor authentication. For more information, read the letter that was sent to clients below.
Read: Passwords: Turns Out We’ve Been Doing It Wrong This Whole Time
How To Enable Two-Factor Authentication
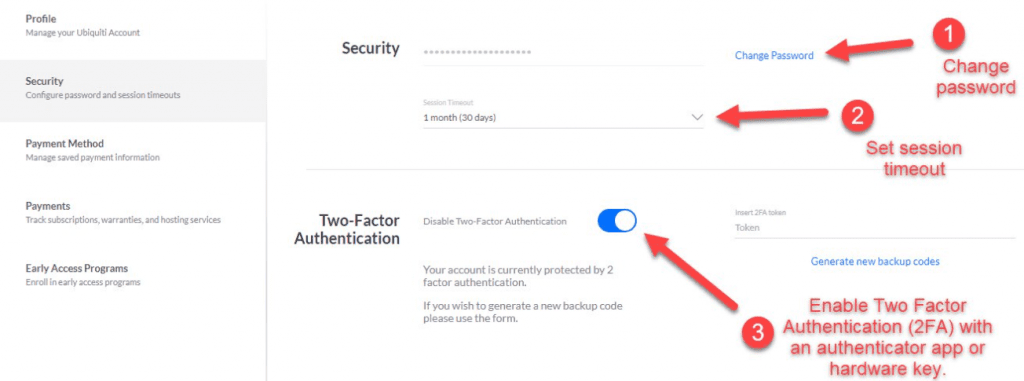
It is extremely important to enable two-factor authentication. Doing so adds an effective layer of security. To set your two-factor authentication up and manage all other security settings, simply visit https://account.ui.com and log in. Once there, you will click on the “security” option from the menu on the left. Next, change your password, set a session timeout value, toggle the switch to activate two-factor authentication. The picture below, which is from twitter.com/crosstalksol, provides a great visual representation of the steps needed to take to protect your organization and your clients.
Read: Can A Cybercriminal Crack Your Company’s Network?
How To Update Your System’s Firmware
Another step you can take to protect your devices is to update firmware. You can find assistance to help you make the necessary updates on the Ubiquiti website. Otherwise, you can follow the steps below:
How To Update Firmware Of ‘AC Devices‘
Step 1: You must first download the correct device firmware for AC devices. Be sure to verify that it is the newest firmware available for your device.
Step 2: Click on the “Settings” button on the left-hand side of your program’s Dashboard.
Step 3: Next, you will need to navigate to the “System” tab of the device you wish to upgrade.
Step 4: Under the “Firmware” section, click on the “Upload” button and proceed to upload the firmware that was downloaded in Step 1.
Step 5: Upon the successful upload of the firmware, it will be thoroughly checked to ensure compatibility. When this concludes, an “Update” button will appear.
Step 6: Finally, simply click on the “Update” button and wait for your device to come back online.
How To Update Firmware Of ‘M Devices’
For those of you with M Devices, you will want to follow the following six steps.
Step 1: Similar to the above example, you will begin by downloading the necessary firmware for M Devices. Again, verify that the firmware you are downloading is the newest version available.
Step 2: Next, navigate to the “System” tab of the device you would like to upgrade.
Step 3: Then, under the “Firmware” section of your device, click on the “Choose File” button and proceed to upload the firmware that was downloaded in Step 1.
Step 4: At this point, you will click on the “New Upload” button.
Step 5: Upon completion of the upload, the file will be thoroughly checked to ensure that it is compatible with your device. Once it has been verified, an “Update” button will appear.
Step 6: Finally, click on the “Update” button and simply wait for the device to come back online.
Read: On Your Guard
Additional Assistance
Here at Rea & Associates, we take cybersecurity and data protection very seriously. Therefore, we are more than happy to assist you in ensuring that your organization is protected. If you are having any issues related to this Ubiquiti breach or any other security concerns, please reach out to the Rea cybersecurity and data protection team today.
By Travis Strong, CISA (Wooster, OH)
Looking for additional cybersecurity and data protection insight? Check out these resources:
Article: ‘Ink Is Cheap. Legal Defense Is Expensive’
