Doug:
From Rea & Associates studio, this is unsuitable. A management financial services podcast for entrepreneurs, tenured business leaders, and others who are ready to look beyond the suit and tie culture for meaningful measurable results. I'm Doug Houser. On this weekly podcast thought leaders and business professionals break down complicated and mundane topics, and give you the tips and insight you actually need to grow as a leader while hoping your organization to grow and thrive. If you haven't already, hit the subscribe button so you don't miss future episodes. And if you want access to even more information, show notes, and exclusive content, please visit our website at www.reacpa.com/podcast and sign up for updates.
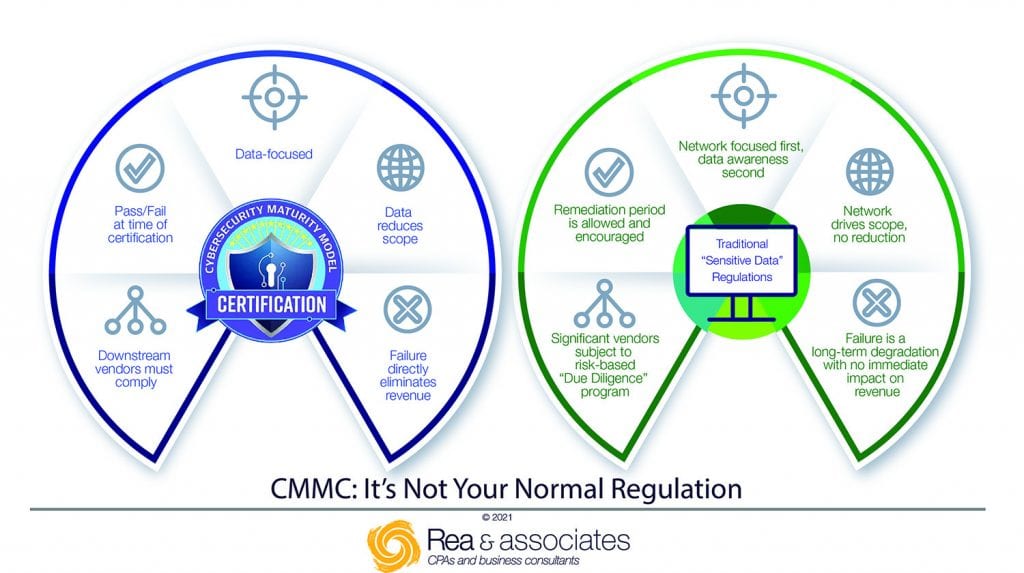
Cyber threats and data breaches are making the news more and more. And it's a terrible thing when it happens to any or all businesses, certainly. But when your business does work for the government, it's particularly bad. It's a national security issue. The Department of Defense recently implemented the Cybersecurity Maturity Model Certification to help protect America as a whole, as well as businesses that do work for the Department of Defense. Ty Whittenburg], a senior team member on Rea's cybersecurity and data protection team is here to explain what CMMC is, what it means for businesses, and how business owners can implement the processes necessary to achieve the proper certification. Welcome back to unsuitable, Ty.
Ty:
Hey Doug, thanks for having me again. Really appreciate it.
Doug:
Oh, always. It's always a pleasure to have you on, and I always learn so much and at the same time, it kind of scares me too. Because you see all this stuff out there and it's obviously in the news more and more as we said in the opening. We saw that with the pipeline couple of months ago. You can go back to solar winds and... But I think part of the misnomer here is that "Gosh, they're really only after the big companies." And certainly, we'll get into this with the CMMC, but it's really everybody who needs to be aware of this, correct?
Ty:
Certainly, most certainly. If you are doing business and you're lucky enough to not have to use any type of electronics or technology then you could consider this a blessing. But if you're the other 95% of us that rely on email, rely on Slack or Microsoft Teams, or having to share data across organizations, then you're feeling the pain right now.
Doug:
Yeah. And speaking of which, myself dealing in construction and commercial real estate, they were often an afterthought and it's, "Ah, nobody cares about a $20 million a year HVAC contractor." Or, "They're not that sophisticated. What's the big deal?" I know we've had some instances certainly recently where clients and prospective clients have gotten hit. And I think part of the interesting thing with this whole CMMC certification process is that it applies to everybody, regardless of size. Correct?
Ty:
Correct. Regardless of size, the defense industrial base is huge when you think about it. You talked about construction, there are construction companies that are in the defense industrial base to do business with the DOD. As a matter of fact, I think Rea even has a couple of clients that dabble in that particular sphere. And so no longer can you say, "I'm a small fish in a big pond." I think if you think back to the situation that happened with the HVAC company that was working with Target and [inaudible 00:04:10] was on the same network as the credit card company. Long gone are the days of saying, "Well, nobody wants me." I guess you are the belle of the ball now, no matter what type of... $20 million or not.
Doug:
Yes absolutely. So when we think through these CMMC requirements, it's not necessarily just a direct relationship with the government. Is it? You can be kind of an indirect provider and still fall under these guidelines. Is that so?
Ty:
Most definitely. So your primary contractors everybody thinks of the Northop Grummans or the Sikorskys, the Phillips of the world that have contracts with the government, but the reality is they just like the rest of the world rely on small business, specialty shops, and manufacturing or in any other industry. I guess you can name around clothing and all of that stuff, that they rely on those folks to help build parts of what our government needs. Whether it be for defense or it'd be for retail. And so these small folks have to be in compliance because of that relationship to a federal contract or in some cases have an access to things around what we would call controlled unclassified information.
Doug:
So talk a little bit about that then. If I'm somebody says maybe even two or three steps down the line and I'm a fairly small, maybe niche manufacturer or contractor. Now all of a sudden I hear this CMMC, what does that mean for me in terms of what has to do and deadlines? When do I have to adhere to it and all that?
Ty:
That's a great question. And so a lot of folks if you're a business leader and you stay on top of your governance around IT, which is tied into your procurement process, then you were proactive with this. You're in the tabloids that talk about DOD information around acquisition or defense contract information and saw the CMMC conversations happening in 2018 and then 2019. And so you saw the future. Otherwise, you're on the other half or the other side of the pond where it was a trickle-down effect. Your primary said, "Hey, in order for me to continue to do business with you, you have to submit this self-assessment. With that self-assessment you have to have what's called a system security plan and a plan of action milestones: on how you're going to achieve the Cybersecurity Maturity Model Certification, that's appropriate for this contract."
So we've had a couple of clients where it's kind of been the latter. They got notified that they needed to update their NIST 800-171 self-assessment. And they needed to start preparing to achieve whatever maturity level it was. And in this particular instance, the one I'm talking about is maturity Level 3. So if anybody's been doing business with a prime and they're a sub, or they're a sub of a sub: they've had to submit a self-assessment of the NIST 800-171. And they've had to put it into the procurement portal, what they call SPRS. And then if they haven't done that, holy smokes, they need to get on top of it.
Now you said timeline, so when you think about timeline nothing in the government moves at the speed of a Usain Bolt or any future track star out there. So the DOD was smart about this. They said, "Hey..." They did a request of information in October 2019 for the long-term implementation of sustaining the growth for the Cybersecurity Maturity Model. And that RFI was seeking an independent body to help oversee the management of CMMC. So those were kind of the first steps. And then after November 2019 meeting with the DOD, the non-profit Accreditation Body was put together. So now you lead forward, we get into 2020 and they create some supplemental things around that. And the forces behind all of this create the Cybersecurity Maturity Certification Accreditation Body. And that Accreditation Body org is in partnership with the department of the Undersecretary of Defense for Acquisition and the DOD rolled in place to CMMC model. So-
Doug:
Gotcha.
Ty:
Crawl, don't walk, right? So-
Doug:
Right. And so I know we have you and a couple of colleagues have this certification, which not a lot of folks do at this point. And again, if I'm a typical small owner-managed business, our client base this now it's in front of me. It could really impact me, prevent me from bidding on opportunities. And at the same time, if I get ahead of the game and get on this now it could potentially be a competitive advantage for me as well. Right?
Ty:
Right. It could definitely be a differentiator versus being a negative delta. You could turn it into a positive Delta. Some of the things that the Department of Defense said with that is, "Everybody who gets a government contract by the end of the fiscal year 2026, anybody that does business in the space with the Department of Defense will need to have some maturity level." Between either maturity Level 1: which will allow them to see federal contract information. Maturity Level 3 is where the biggest brunt of everybody in that defense industrial base will be. Where they'll need to have that maturity Level 3, where they can have access to controlled unclassified information. And then there's maturity Levels 4 and five, which they're still trying to iron out. And I think there'd probably be some things around that around security clearances as well too. There was even some discussion with Katie Arrington in a podcast that she did, where there might even be in maturity Levels 4 and five. Maturity Level 4.1, 4.2, 4.3. Yeah, getting that granular.
Doug:
So better to get the experts like you and our team involved for sure.
Ty:
Most definitely. I think you want to be ahead of this versus behind it. There have been tons of folks in the industry, big companies that if you think about the relationships that we have, internet providers and stuff like that in the European theater around GDPR and stuff like that, that drag their feet. Unlike GDPR, you can continue to do business and kind of roll the dice of whether or not you get fine. But this has a direct monetary revenue impact on businesses if they are not complying with CMMC.
Doug:
So we talk about preparing for this. You've mentioned a couple of times a system security plan. What exactly is that and what's in it? How does one put all that together with our assistance?
Ty:
Yeah. So I never want to come across as blasphemous, but it's almost the Bible of your IT technology, your policies, your procedures, and your process. And it can be a lengthy document. It talks about who owns what process. Is it implemented and if it's not applicable to you? And then not only do you have a direct policy... Everybody has an employee and a handbook for the most part. "You can do this when you're on company time, you can't do this. This is what sick days look like." Think of it like that. This is your marching orders for how you do business with your IT and how you control that information you have access to. And depending on your maturity level, maturity Level 1 does not require a system security plan. So if you're a small business, a mom and pap, or a family business that works in the specialty for a particular vendor in the DO space or DOD space, or directly with them. As long as you have some ad hoc things in place, you're okay.
But the minute the RFP has controlled unclassified information in it, you have to demonstrate this culture. And the SSP kind of maps that culture for you around what's the policy? How do people do it? If you and I were to walk into a business tomorrow that needed to be at maturity Level 3 and we needed to see that for physical security when somebody enters the building, you have to get a visitor's badge. You have to sign in, you have to turn that badge back in. All of those processes have to be written down and demonstrated, not only through a piece of paper saying that you do it but through your own actions. You have to walk your talk.
Doug:
And we've run into this. And I know you see a lot of companies, small, mid-sized owner-managed businesses say, "Well, I have a managed service provider that does this. Does my IT for me. I'm sure they're on top of this and they've got this covered." But that's obviously not the case, is it?
Ty:
No. What's the leadership thought process around situational leadership? You direct, you coach, you support and you delegate. This is one of those where owners of businesses can't just delegate. They still have to maintain some form of leadership over the direction that coaching and that directing the piece, they need to be informed. My dad, I love him to death, drove me nuts as a teenager when he used to say, "Ignorance of the law was no excuse." Ignorance of what's going on with the IT in your organization, whether you be large or small is no excuse. And larger org and public corporations have things like Sarbanes-Oxley, GLBA that kind of managed them.
CMMC is bringing that to a whole new level I think, whether you be a small business, a medium-sized business, or even a large enterprise. It is a level playing field around ensuring that those people out there who want information around what our government does or how we build what we build do not get easy access to it. Sort of like our president kind of putting his foot down if yesterday where he said, "If you use cyber, we'll respond with cyber." And I'm not saying that we're getting to that particular point, but I think leaders in business nowadays have to be much more cognizant of what their digital footprint is. What their data sovereignty is. And not be very cavalier about how they would have operated in the past and just kind of turn it over to somebody else to do it all, and wash their hands of it.
Doug:
Yeah. We see a lot of things like this, where companies maybe don't want to put the additional processes and procedures in place. Because they're... It's, "Oh well, it's kind of a pain. I don't want to go to multifactor authentication. Hell, I can't... I can only remember so many passwords and blah, blah, blah." So where do you start when you have a company like that? Do you go in and do kind of an initial assessment? Where do you start with this process?
Ty:
So that's a great question as well. I think for us, the self-assessment form, the NIST 800-171 really kind of sets the roadmap for how you engage that. That becomes your gap analysis. Some folks when you think of in accounting world, you think about audits and stuff like that. Our team participates with our audit team around looking at the IT part of the financial side of the audit. Well, this 800-171 gets pretty deep like that as well too. And depending on what particular level you need to be at, we can identify are you doing these things ad hoc, is your organization risk-informed? [Inaudible 00:16:31] doing them at a relative level, are you building into that particular space? So there's a lot of things that go into that. You can't just buy a software solution or a piece of equipment and think that you're going to be there.
We're looking at all of it, the logic behind the software. We're looking at the hardware. We're looking at the cultural aspect of it. How your people employ it day in and day out. It's almost as if you're as the Japanese we'll call it, "Standing in the circle." Like a kaizen event. And the Japanese call it Gemba. I don't want to mess that up or maybe it's Gemba. Where you stand in the circle and you go to the place where the work happens and you observe it. And if you're not doing those things, then this 800-171 uncovers it. And then it allows you to identify those gaps and talk about controls that you need to put in place in order to ensure you are doing the correct things. To not only safeguard the government, but really in the end you're safeguarding your intellectual property. And ensuring a dedicated revenue stream to you that can be pretty beneficial to a lot of folks. Because as we all know, the government likes to buy a lot of stuff.
Doug:
Yeah. And that's the thing too. We try to talk to clients about this. At some point when you are looking to transition your business, particularly if you're looking at some type of third-party transaction. Whether it's to somebody else in the industry, a strategic buyer, private equity, whatever; they're going to really pay attention to these things. Because if you've got again, good processes and procedures in place that enhance the value of your operation. Right?
Ty:
Exactly. And you know what, if you're looking for cyber insurance, if you're a good driver and you have a good credit rating, you get the better driving discount on your insurance.
Doug:
Absolutely.
Ty:
Well, if you've taken your cyber seriously and you need to get cyber insurance, that should have some positive impacts for you there. And depending on your state, Ohio has the Ohio safe harbor law, S.B. 220 that states are more business-friendly than consumer-friendly. Around if you've been doing your due diligence to safeguard sensitive information, whether that'd be personally identifiable. We're talking about control and classified information. But these organizations, if they're doing these things, can help protect them from potentially reduce the impact of lawsuits as well too.
Doug:
Yeah, absolutely. So once you've gone in or assisted say with an assessment, and you've got this gap analysis. How then does a company go about implementing the things necessary to meet the CMMC requirements and demonstrate full compliance? How do you proceed from there?
Ty:
Well if we've come in and done the gap analysis, we've become pretty intimate with that client as well too. We've identified the gaps. We can pretty much put together a high-level plan of action milestones for that. Now your question was, "Well, how did they go about doing that?" Some folks may try to go at it themselves to get to that maturity level. I liken it to, if you've never had to do any plumbing for your house, change out the filter on your AC unit or better yet in this modern-day age install a Nest Thermostat in your home: you go out and hire somebody who's an expert. This is what they do day in and day out. Hopefully, you don't represent yourself in court. And if you're a large business, you don't do your own taxes. You get a Rea to help you with that because we can navigate the waters. Same in cyber.
So a lot of times, if you don't want to dedicate the manpower to it or you don't have an IT team, or it's not in the wheelhouse of your managed service provider, a registered provider organization: which Rea is, can go in and literally from that gap analysis start helping you put policies and procedures in place. Help you write that 40-page document or 50-page document that a system security plan may be. But more importantly, walk-in lockstep with you to make sure you're getting to the goals that you need to. Always I talk to folks sometimes I tell them it's like a Red Rover as a kid. Our arms are interlocked and you can break through if we're in lockstep, we'll get you there and we'll get you there safely. But you have to be open to change and your culture has to be prepared to make some of those pivots. And culture takes time. So don't think this will be an overnight process.
Doug:
Yeah, absolutely. Well, I love all these great analogies you've come up with Ty. It's always my favorite part to talk with. Did you get all that from your military background, or is that just innate for you?
Ty:
Well, I think part of it has gotten better as I age. The things that I got from the military, you and I have to talk about some time when we're having a beer or a bourbon together.
Doug:
I like it.
Ty:
It's not appropriate for radio or [inaudible 00:21:45] podcasts. No, that's not true. I had some great leaders in the military and it taught me a lot. Taught me a lot about discipline. Really taught me a lot about integrity and building that relationship with folks. But the analogies, I think it comes out. I work with a great group of guys. You know [Sean 00:22:03]. And then the other thing is if you can communicate with people in a way that doesn't get super technical, it takes all of the fuzziness out of it and engages people a little bit more. Folks know Red Rover folks, folks know the belle of the ball, know the prom king and the prom queen. So you can make a difference with folks when you speak a common language versus TCP, IP, SSD. As soon [crosstalk 00:22:32] doing all that stuff, people tune me out really, really fast.
Doug:
Yeah. Well said. And that's great insight, I love it. The bottom line is if anybody... If you even think you're touching the government in any way, you better give us a call and talk to Ty and our team of experts. And see where you need to be and how we can help you with a roadmap to get there.
Ty:
I would just add one thing if I could.
Doug:
Sure, absolutely.
Ty:
One client that we were doing business with, stopped getting business from their prime because they hadn't done the self-assessment. Now I didn't ask them for dollars and cents, but since we did the self-assessment for them and submitted it in SPRS, the primary they have won 18 new contracts since the end of March when we engage with them. So that's a huge win. That's an investment where they weren't getting any money. And now they are generating much more revenue.
Doug:
That's awesome. Yeah, a great story there for sure. Well, thanks Ty and we'll look forward to having you on again. I appreciate your insight as always. And certainly, if you want more business tips and insight, or to hear previous episodes of unsuitable, visit our podcast page at www.reacpa.com/podcast. And while you're there, sign up for exclusive content and show notes. Thanks for listening to this week’s show, be sure to subscribe to unsuitable on Apple Podcasts, Google Podcasts, or wherever you're listening to us right now, including YouTube. I'm Doug Houser, join us next week for another unsuitable interview with an industry professional.
Disclaimer:
The views expressed on unsuitable on Rea Radio are our own and do not necessarily reflect the views of Rea & Associates. The podcast is for informational and educational purposes only and is not intended to replace the professional advice you would receive elsewhere. Consult with a trusted advisor about your unique situation, so they can expertly guide you to the best solution for your specific circumstance.